I've put some new rules in place around passwords for whenever you're next updating your password (you do update your passwords, right? Right?).
We are now using:
We are now using:
- Dropbox/Dan Wheelers's zxcvbn, a "password strength estimator inspired by password crackers. Through pattern matching and conservative entropy calculations, it recognizes and weighs 10k common passwords, common names and surnames according to US census data, popular English words, and other common patterns like dates, repeats (aaa), sequences (abcd), keyboard patterns (qwertyuiop), and l33t speak.
Consider using zxcvbn as an algorithmic alternative to password policy — it is more secure, flexible, and usable when sites require a minimal complexity score in place of annoying rules like "passwords must contain three of {lower, upper, numbers, symbols}"."
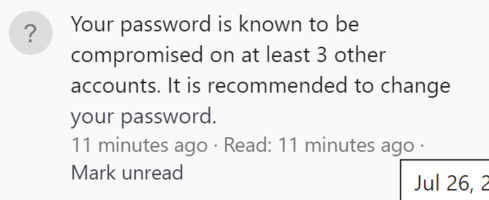
- Troy Hunt's Pwned Passwords service, to protect against password reuse and credential stuffing. "Password reuse is normal. It's extremely risky, but it's so common because it's easy and people aren't aware of the potential impact. Attacks such as credential stuffing take advantage of reused credentials by automating login attempts against systems using known emails and password pairs. The Pwned Passwords service was created in August 2017 after NIST released guidance specifically recommending that user-provided passwords be checked against existing data breaches . The rationale for this advice and suggestions for how applications may leverage this data is described in detail in the blog post titled Introducing 306 Million Freely Downloadable Pwned Passwords. In February 2018, version 2 of the service was released with more than half a billion passwords, each now also with a count of how many times they'd been seen exposed. "
- Look! It's a password strength indicator.
- Minimum password length of 8 characters